In all likelihood, I was not the only one last class who wanted to discuss further the issue of online identity and privacy. I tend to agree with Kashmir Hill in her suggestion (in class and in her website) that our sense of privacy will change. Yes, in a more transparent era, or perhaps just for a younger generation, last Friday’s embarrassing moment will remain just that and no more, despite and perhaps in part due to online evidence.
This perspective may be comforting, but we should qualify this comfort. It is a small, finite comfort.
The comfort lies in the realization that our own mistakes will not be as damaging as we might initially fear. Mr. Scalia (who often seems to be assigned in readings at Yale at his expense!) if little else in our readings does seem to remind us that the idea of the law protecting every little fact about us is absurd. Kashmir Hill suggested that more openness might lead to more comfort. And indeed, for stuff like what happened last Friday that a friend posted with you tagged in it, it might be less silly to turn to social norms than to turn to law. Social norms are formed online — we all have seen this happen in our generation — and we can expect a great deal of such online exposure to be made safer by online social norms, without overprotective, “silly” legislation. We can all simmer down now because the privacy FUD problem is solved.
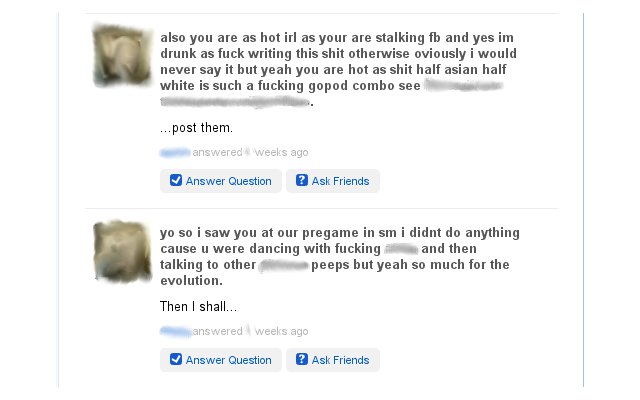
If that leaves you less than satisfied, I’m with you. “Online exposure” can go far beyond being tagged in a Facebook pic. Specifically, your online exposure is not necessarily of your own doing, or even your friends’ doing.
Daniel Solove’s blog post in this week’s reading suggested an interesting term: Aggregation. Solove uses this term to describe a way that gathering data on someone can lead to violating his/her privacy, essentially by connecting “innocuous” points into a “detailed portrait of our personalities and behavior.” We can ask a sort of philosophical question: What other effects might the Internet bring about to data about you?
Like Seth Godin’s list of ways things can get broken, my list of privacy FUD is sure to be incomplete. Please comment and add your own!
1. Aggregation – Connecting innocuous dots can lead to an uncomfortably detailed big picture. For an example, do the readings.
2. Dis-gregation – Less is more — more harmful.
What if an online journalist or a Facebook friend isolated a couple (true) facts about you and leaves out other relevant facts?
3. Context Distortion – Taken out of context, new implications begin to arise.
I thought of this last class when I discovered searching for my name leads to a porn website. No, I don’t have a porn star double life! But in 2009 I did help promote Yale and other US colleges to Japanese students, and the Japanese term 中高生 (middle and high school students) landed links to YouTube versions of our video footage filled the greater part of a fuchsia-colored website. (Incidentally, if you’re being naughty and trying to find this website, at least on the page with my name in it there was nothing graphic, let alone anything involving minors.)
4. Unplanned Anti-Obsolescence – It’s forgotten by now, right? No, it’s in the Net’s hands now.
A friend thought he’d put up a silly status update, and delete it 30 minutes later. It wasn’t something he wanted everyone to know, but having a few know would have been acceptable to him. He had it planned out that way. But when another friend found it hilarious and re-posted it as his status, control over it had changed.
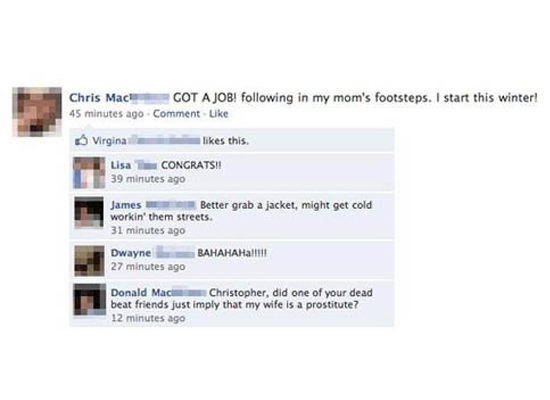
5. Promulgation – Data that’s out there, but in small circulation, can become less innocuous by gaining popularity.
A funny story shared to friends might not be best when shared on the Internet, where there are less degrees of separation from total strangers who might interpret it differently. Cyber-bullying examples come to mind as well — a few enemies at school is a smaller problem when they’re not enlisting online comrades. Or what if RapLeaf had sold (“inadvertently”) data about your online behavior not to a dozen advertisers, but hundreds? What if they also sold data to your workplace, school, or to the government?
I am sure there are more effects we could talk about, but the bottom line is that an embarrassing Friday should not be our only concern. Even if greater transparency helps establish social norms online, we shouldn’t ignore that it’s becoming easier and easier for the Internet to affect info about you. What you post about yourself or reveal to marketers tracking you is really just where that data might start off – really we’re talking about the potential for that data to take on a life of its own. Much of this seems difficult for the law to prevent, but I suspect we’re more eager to turn to the law rather than social norms when we consider that it’s not just about our own mistakes confined to a few popular sites.